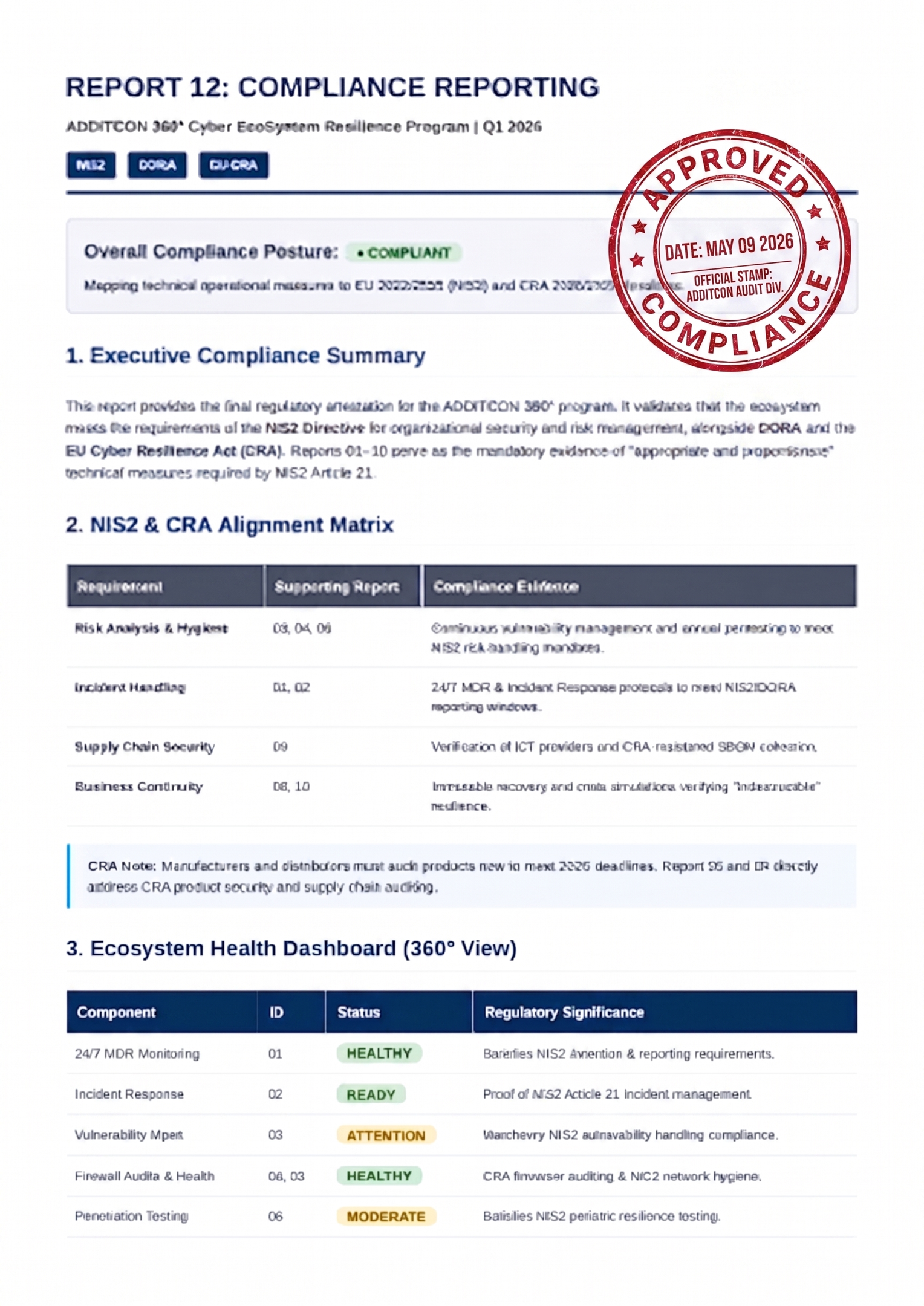
24/7 MDR Monitoring
Meets incident management and detection requirements. Continuous vigilance ensures the organization can identify and respond to threats in real time.
Meets incident management and detection requirements. Continuous vigilance ensures the organization can identify and respond to threats in real time.
Annual Vulnerability Scans: Meets the risk management requirement. Regular scans document that you are proactively working to identify and address technical weaknesses.
Annual firewall audits and health checks: Meets the requirement for network and information system security. It proves technical control over network segmentation and access.
Incident Response Manager (IR): Ensures business continuity. In the event of a breach, a team of experts is ready to minimize damage and quickly restore operations.
Penetration testing: Acts as a validation of the effectiveness of your measures. It proves to regulators that your defenses actually work against real attacks.
Phishing awareness and training: Strengthens the human factor and meets the requirement for security training for staff and management.
Immutable Geographically Separated Backup. Meets the requirement for business continuity and crisis management. By storing data in an "immutable" (read-only) format, ransomware cannot delete the backups. The geographical separation protects against physical disasters (fire, power outage) at the main location.
Strategic meetings and compliance reporting: Supports management accountability. Management receives the reports and decision support needed to demonstrate that they are overseeing security efforts in accordance with the law.
Continuity Planning (BCP), Business Continuity Strategy (BCS) & Crisis Drills
Article 21 emphasizes the importance of having a plan to maintain operations in the event of an incident. Through regular "Crisis Drills" (simulated crisis exercises), you ensure that the organization actually knows how to act when it happens.
Supply Chain & Third Party Risk Management (TPRM)
One of the most central new requirements in NIS2. You must now assess the security level of your suppliers and subcontractors. This is about ensuring that your partners do not constitute a weak link in your own security chain.
360° Cyber Ecosystem Resilience Program gives you the security and evidence to be audit and compliance ready, these services with our reports give you